-
-
Platform
-
Company
-
-
-
Commercial
- Industry Collaboration
- Solutions
- Industries
-
© 2025 Fortress Information Security. All rights reserved
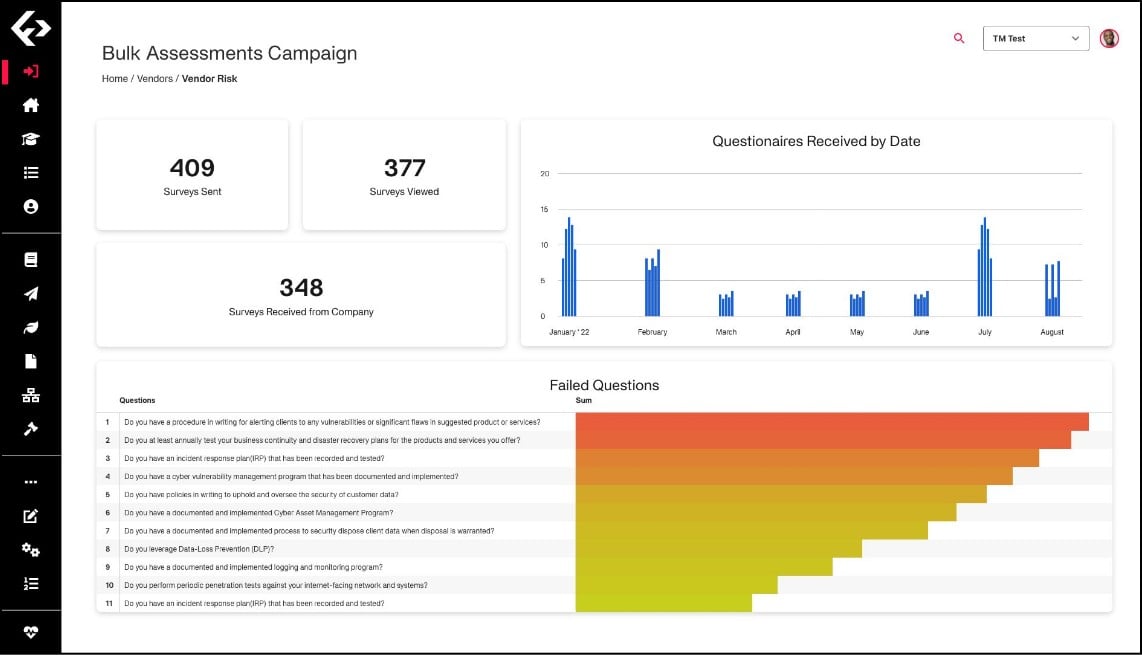
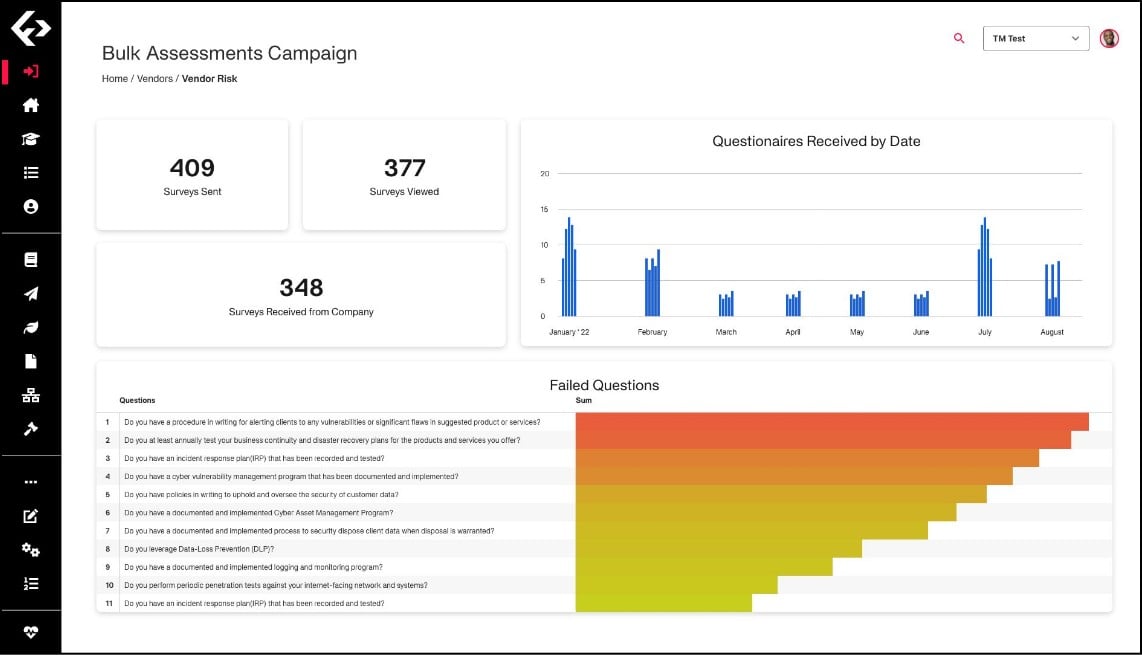






Conclusive Results
Provides customized solutions utilizing sector-specific best practices.
Encourages shared data sourcing for collective risk solving.
Instantly elevates the sophistication of security programs.
Drastically cuts down time to remediate or mitigate vulnerabilities.
What Our Customers Say
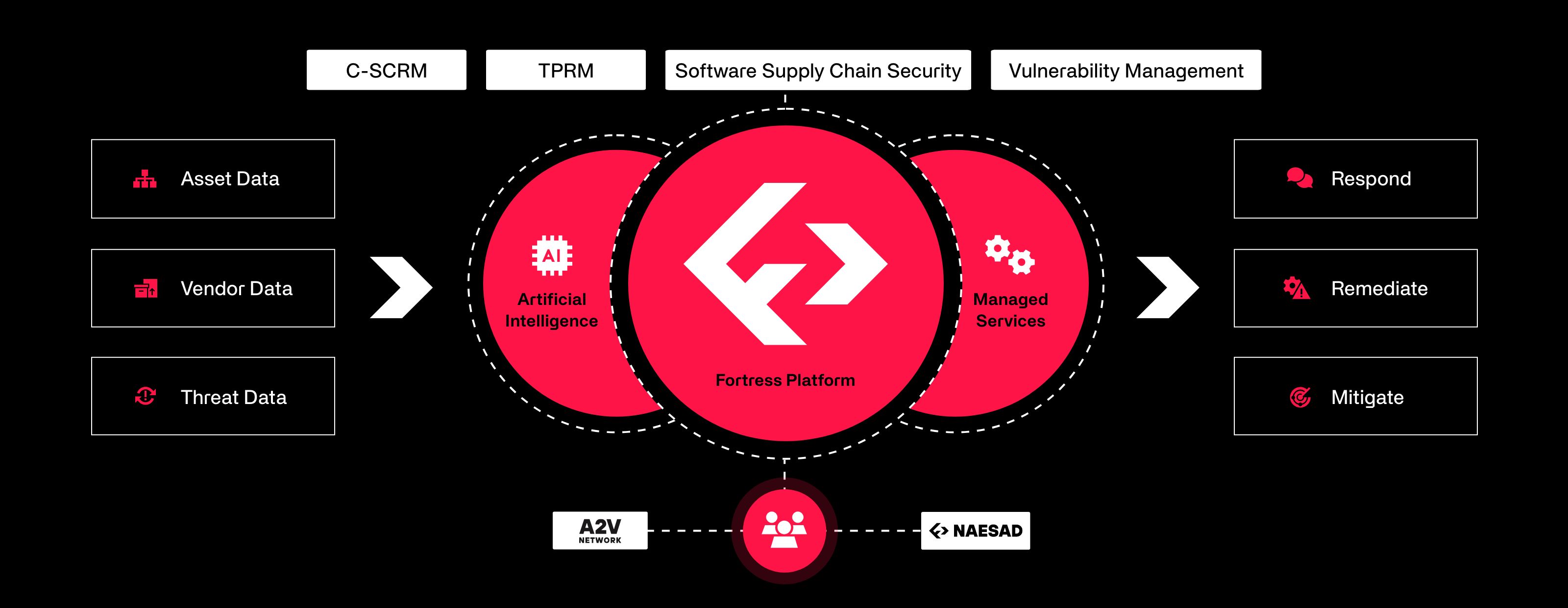
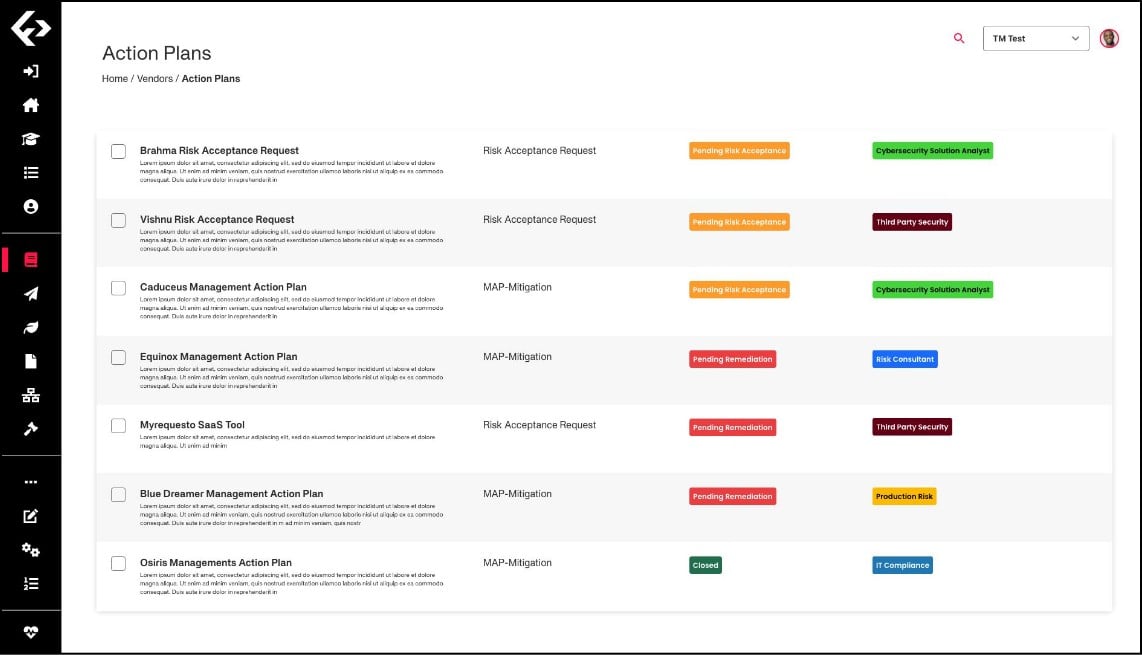
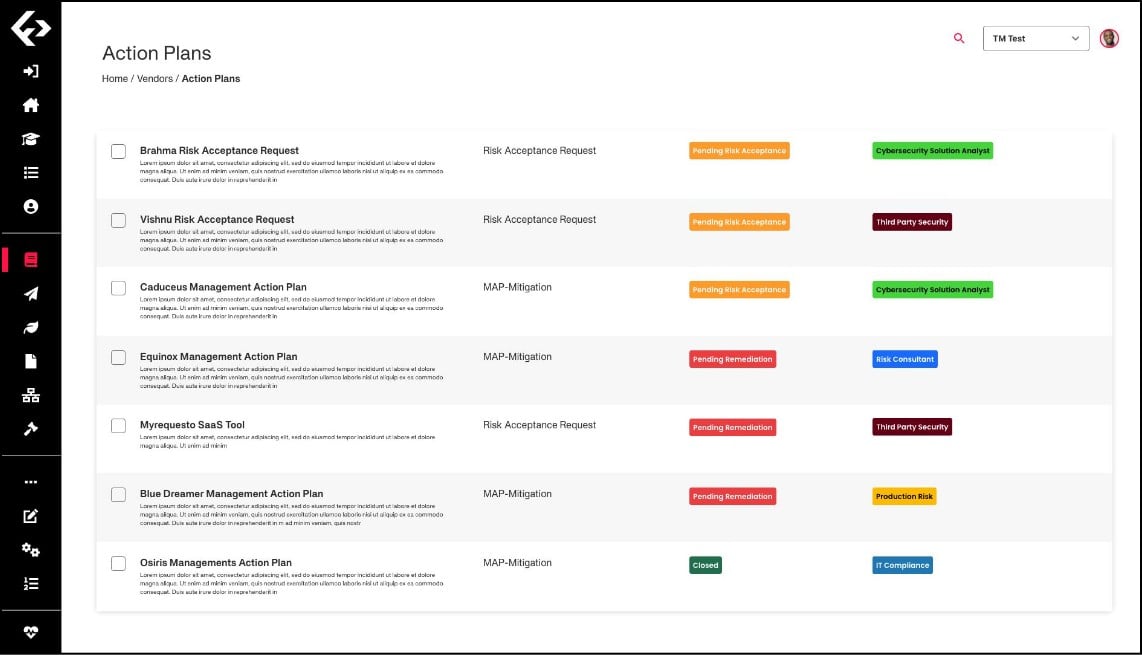
The Fortress Platform is a risk management workflow system designed to not just identify risk, but prioritize and resolve it. The platform guides users step by step through the full lifecycle of supply chain risk management.
The Fortress Platform identifies vendors, products, and assets, evaluates their risks, then sets up workflows for resolution — whether internal fixes or vendor collaboration — with continuous monitoring.
The Fortress Platform provides transparent, customizable scoring. Customers can use default playbooks or adapt scoring to their own risk posture, covering vendor assessments and vulnerabilities.
The Fortress Platform supply out-of-the-box playbooks with clear remediation steps for IT, OT, and cloud environments, helping customers and vendors address gaps efficiently.