-
-
Platform
-
Company
-
-
-
Commercial
- Industry Collaboration
- Solutions
- Industries
-
© 2025 Fortress Information Security. All rights reserved
Vulnerability Management
The Fortress Platform proactively secures OT, IT, and IoT devices before vulnerabilities can be exploited, safeguarding data and maintaining the integrity of tech infrastructure.
Fortress’s vulnerability management solution ensures cyber resilience in complex operational environments to identify and remediate cyber issues quickly and efficiently. Fortress vulnerability management is the only cybersecurity tool your enterprise organization needs to manage the vulnerability lifecycle.
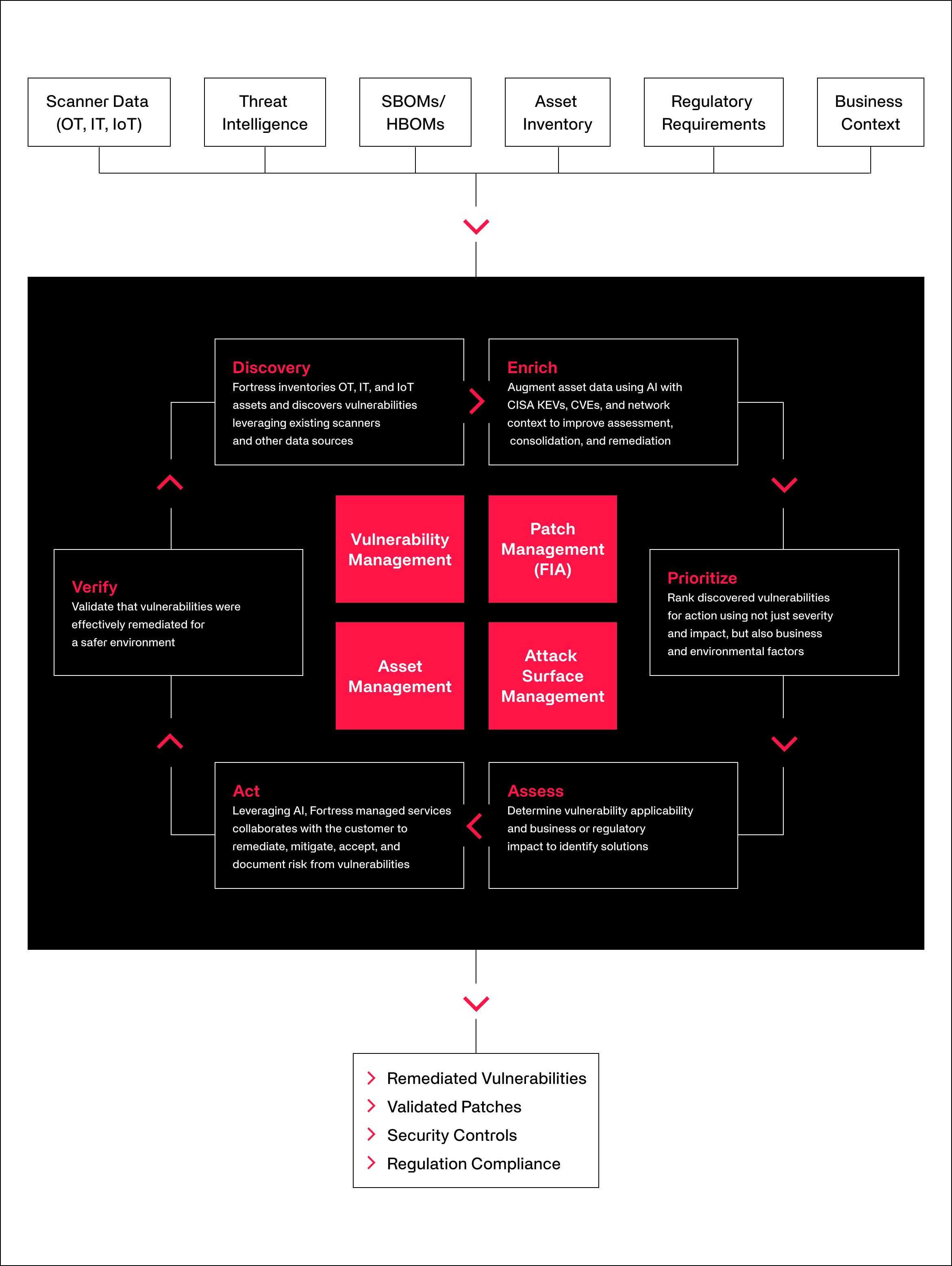
Most vulnerability managers are limited to ingesting scanner data and providing basic remediation steps. Fortress goes beyond basic by providing an advanced vulnerability management platform that ingests data from scanners, threat intelligence, software and hardware bill of materials, regulatory requirements, asset inventories, and business context resulting in a 360-degree view of your security posture. This data, combined with Fortress managed services, enables unparalleled cybersecurity protection for companies with critical infrastructure.
Speak with an expert to learn about our comprehensive vulnerability solution.
Fortress managed services researches zero-day vulnerabilities and enables advanced incident management for mitigating risks and resolving vulnerabilities.
Critical infrastructure organizations, such as utilities and oil and gas, have specific requirements (such as NERC CIP for utilities) that Fortress is prepared to handle.
Fortress expert managed services can be more cost-effective than maintaining or expanding an in-house team, as it reduces the need for constant training, tooling, and staffing.


Fortress enables a truly comprehensive vulnerability management program that not only leverages scanner data, but also bill of materials, patch data, regulatory requirements, and business context for remediating vulnerabilities.
To ensure effective remediation, Fortress managed services take on day-to-day operational vulnerability management tasks, allowing organizations to focus their resources and expertise on strategic cybersecurity initiatives and risk mitigation strategies.
Finding, prioritizing, and ensuring remediation of critical vulnerabilities is what Fortress does best, enabling organizations to effectively and conclusively secure OT, IoT, and IT infrastructure.